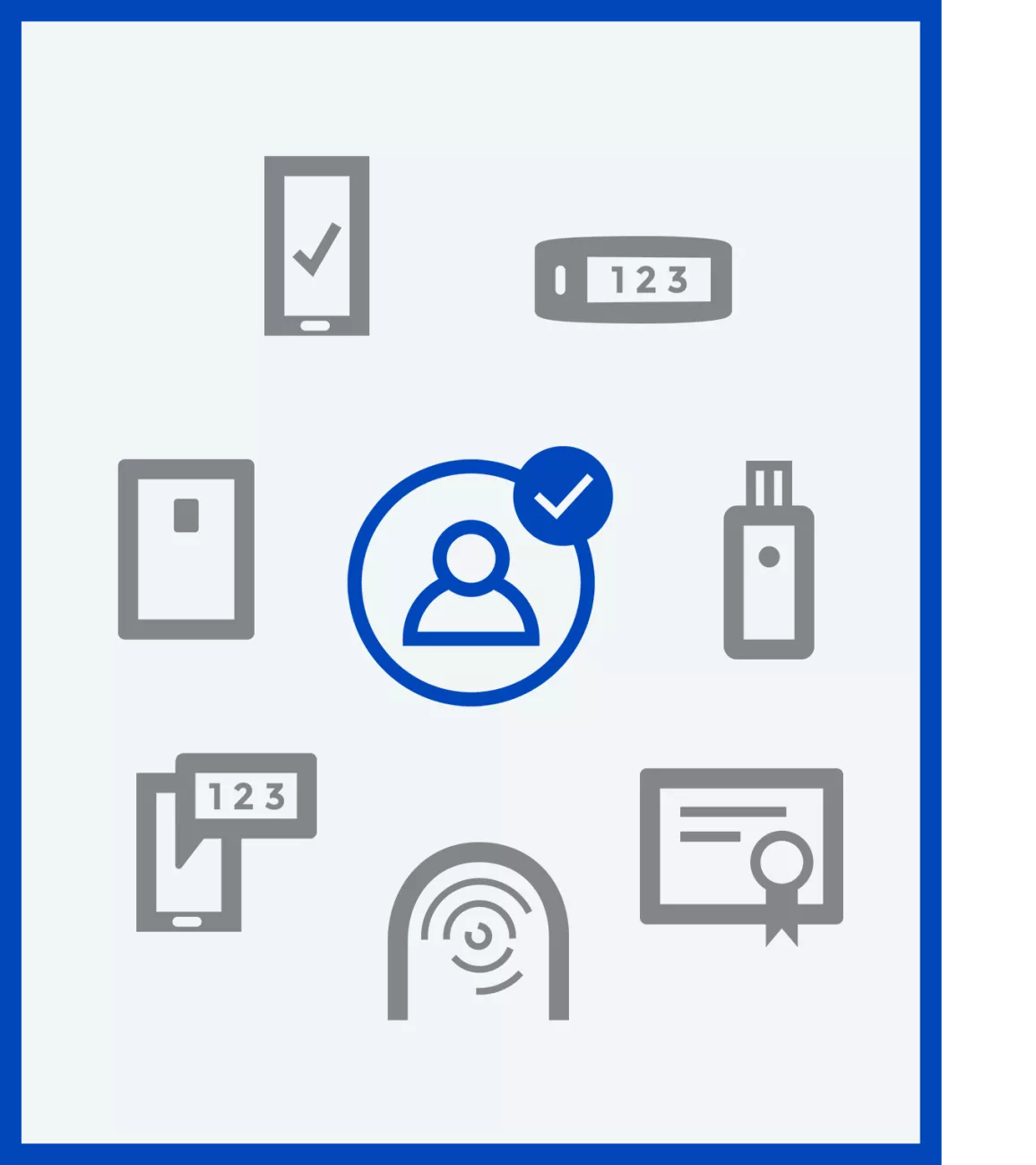
Multi-factor authentication significantly increases the security of your organization. That is the main reason for implementing it. Many legal, financial, medical, and governmental industries require it. Legal requirements, like GDPR and PCI-DSS, also require secure authentication. It acts as the first line of defense for everything in your organization.
By enabling one or several additional factors for authentication, you lower the risk of data leaks, intrusion, and other risks.
To give an example of increased security, we can help you implement MFA so that your company becomes virtually resistant to phishing attacks.
MFA also ties into several other aspects that will make your organization more secure and user-friendly.
It is a vital part of any zero-trust strategy to have secure authentication. Multi-factor authentication also makes it easier for you to enable single-sign-on (SSO) for all your applications in a secure way.
Depending on the authentication factors you choose to enable, you can end user frustration simultaneously. We can help you implement MFA with different factors for different users in your organization, and even help you go passwordless entirely.
Having a secure authentication for single sign-on makes your users more productive when they can focus on their work instead of logging in. We also help you enable self-service for password reset or implement passwordless solutions so that lost or stolen passwords become a thing of the past. SSO with MFA is also essential to enabling secure remote work for your users.
Resources Learn more about our solutions, us, and how we can help you.
Learn more about us
Support Get help with our products and solutions.