IAM made easy — for your needs

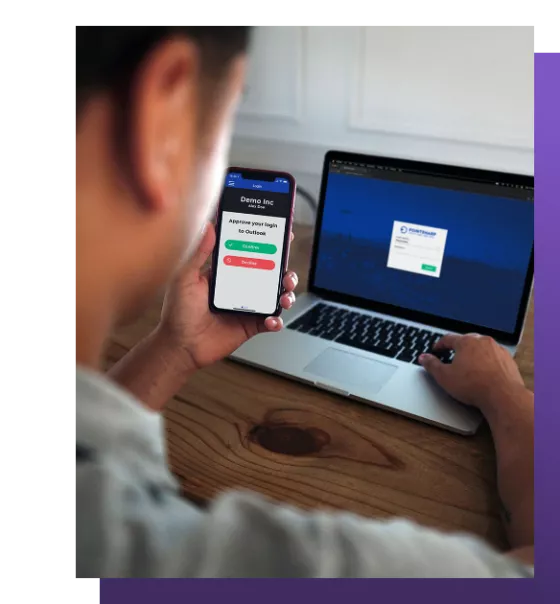
Making sure who has access to what is a core part of any organization, and a core part of security. We can help you streamline the process on all levels, no matter your setup. Everything from creating and managing users, groups, and access to single sign-on and self-service. That makes life easier and more secure for everyone in your organization.
We help you with:
- Comprehensive access management for your entire organization
- Automated identity management
- Enabling remote work without a VPN